Threat actors are leveraging manipulated search results and bogus Google ads that trick users who are looking to download legitimate software such as WinSCP into installing malware instead.
Cybersecurity company Securonix is tracking the ongoing activity under the name SEO#LURKER.
“The malicious advertisement directs the user to a compromised WordPress website gameeweb[.]com, which redirects the user to an attacker-controlled phishing site,” security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in a report shared with The Hacker News.
The threat actors are believed to leverage Google’s Dynamic Search Ads (DSAs), which automatically generates ads based on a site’s content to serve the malicious ads that take the victims to the infected site.
The ultimate goal of the complex multi-stage attack chain is to entice users into clicking on the fake, lookalike WinSCP website, winccp[.]net, and download the malware.
“Traffic from the gaweeweb[.]com website to the fake winsccp[.]net website relies on a correct referrer header being set properly,” the researchers said. “If the referrer is incorrect, the user is ‘Rickrolled‘ and is sent to the infamous Rick Astley YouTube video.”
The final payload takes the form of a ZIP file (“WinSCP_v.6.1.zip”) that comes with a setup executable, which, when launched, employs DLL side-loading to load and execute a DLL file named python311.dll that’s present within the archive.
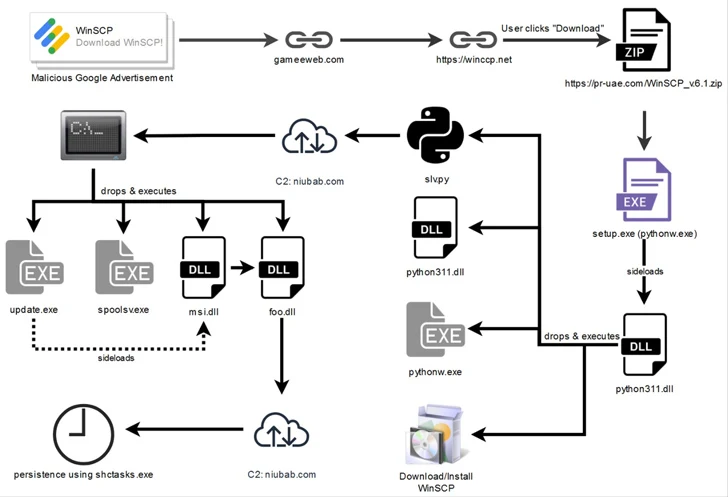
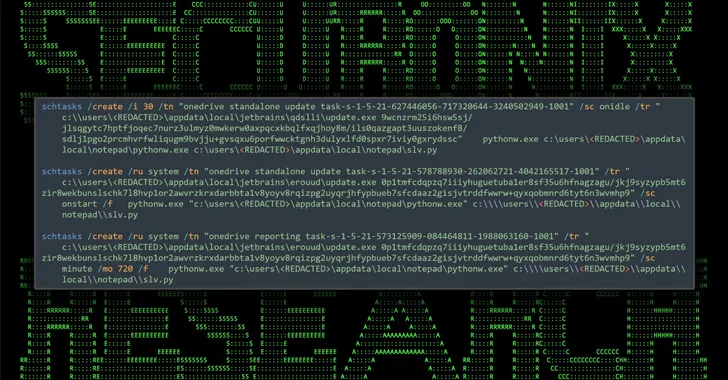
The DLL, for its part, downloads and executes a legitimate WinSCP installer to keep up the ruse, while stealthily dropping Python scripts (“slv.py” and “wo15.py”) in the background to activate the malicious behavior. It’s also responsible for setting up persistence.
Both the Python scripts are designed to establish contact with a remote actor-controlled server to receive further instructions that allow the attackers to run enumeration commands on the host.
“Given the fact that the attackers were leveraging Google Ads to disperse malware, it can be believed that the targets are limited to anyone seeking WinSCP software,” the researchers said.
“The geoblocking used on the site hosting the malware suggests that those in the U.S. are victims of this attack.”
This is not the first time Google’s Dynamic Search Ads have been abused to distribute malware. Late last month, Malwarebytes lifted the lid on a campaign that targets users searching for PyCharm with links to a hacked website hosting a rogue installer that paves the way for the deployment of information-stealing malware.
Malvertising has grown in popularity among cybercriminals in the past few years, with numerous malware campaigns using the tactic for attacks in recent months.
Earlier this week, Malwarebytes revealed an uptick in credit card skimming campaigns in October 2023 that’s estimated to have compromised hundreds of e-commerce websites with an aim to steal financial information by injecting convincing counterfeit payment pages.
Reference: https://thehackernews.com/2023/11/beware-malicious-google-ads-trick.html