The North Korea-linked nation-state actor known as Kimsuky is suspected of using a previously undocumented Golang-based information stealer called Troll Stealer.
The malware steals “SSH, FileZilla, C drive files/directories, browsers, system information, [and] screen captures” from infected systems, South Korean cybersecurity company S2W said in a new technical report.
Troll Stealer’s links to Kimsuky stem from its similarities to known malware families, such as AppleSeed and AlphaSeed malware that have been attributed to the group.
Kimsuky, also tracked under the names APT43, ARCHIPELAGO, Black Banshee, Emerald Sleet (previously Thallium), Nickel Kimball, and Velvet Chollima, is well known for its propensity to steal sensitive, confidential information in offensive cyber operations.
In late November 2023, the threat actors were sanctioned by the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) for gathering intelligence to further North Korea’s strategic objectives.
The adversarial collective, in recent months, has been attributed to spear-phishing attacks targeting South Korean entities to deliver a variety of backdoors, including AppleSeed and AlphaSeed.
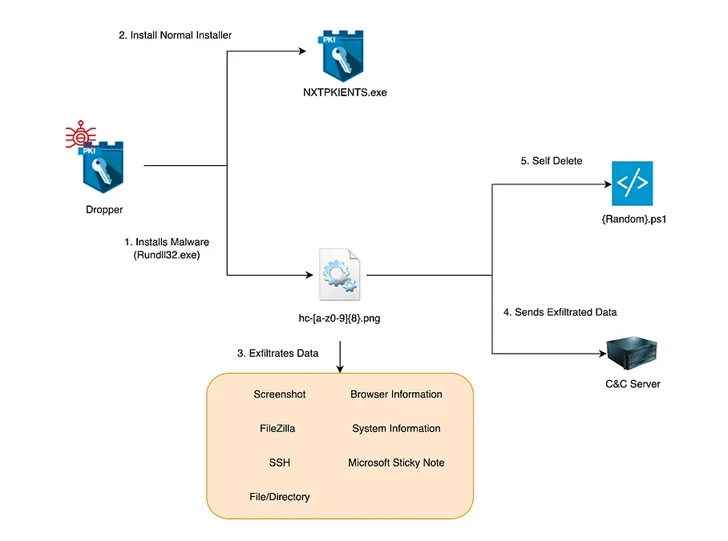
S2W’s latest analysis reveals the use of a dropper that masquerades as a security program installation file from a South Korean company named SGA Solutions to launch the stealer, which gets its name from the path “D:/~/repo/golang/src/root.go/s/troll/agent” that’s embedded in it.
“The dropper runs as a legitimate installer alongside the malware, and both the dropper and malware are signed with a valid, legitimate D2Innovation Co.,LTD’ certificate, suggesting that the company’s certificate was actually stolen,” the company said.
A stand-out feature of Troll Stealer is its ability to pilfer the GPKI certificates issued by the South Korean government from infected systems, indicating that the malware may been put to use in attacks targeting administrative and public organizations in the country.
Given the absence of Kimsuky campaigns documenting the theft of GPKI folders, it has raised the possibility that the new behavior is either a shift in tactics or the work of another threat actor closely associated with the group that also has access to the source code of AppleSeed and AlphaSeed.
There are also signs that the threat actor may be involved with a Go-based backdoor codenamed GoBear that’s also signed with a legitimate certificate associated with D2Innovation Co., LTD and executes instructions received from a command-and-control (C2) server.
“The strings contained in the names of the functions it calls have been found to overlap with the commands used by BetaSeed, a C++-based backdoor malware used by the Kimsuky group,” S2W said. “It is noteworthy that GoBear adds SOCKS5 proxy functionality, which was not previously supported by the Kimsuky group’s backdoor malware.”
Reference: https://thehackernews.com/2024/02/kimsukys-new-golang-stealer-troll-and.html