
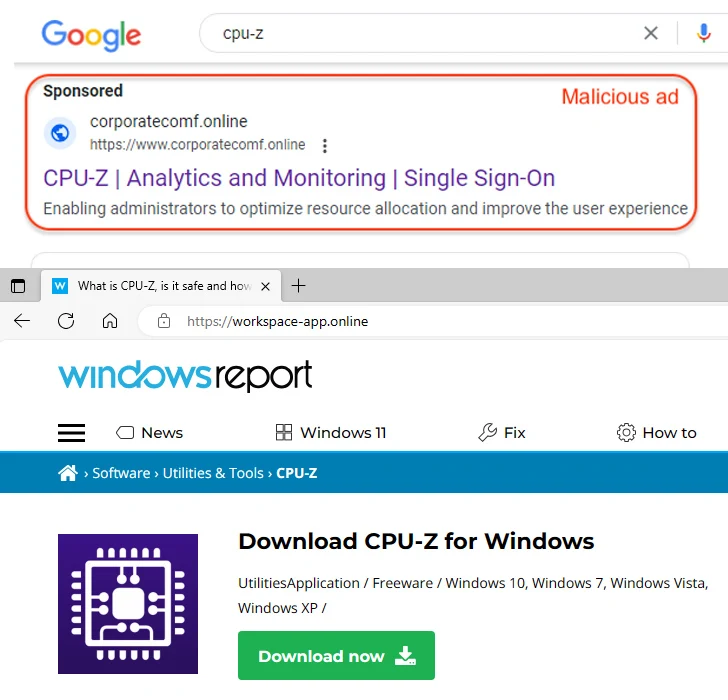
A new malvertising campaign has been found to employ fake sites that masquerade as legitimate Windows news portal to propagate a malicious installer for a popular system profiling tool called CPU-Z.
“This incident is a part of a larger malvertising campaign that targets other utilities like Notepad++, Citrix, and VNC Viewer as seen in its infrastructure (domain names) and cloaking templates used to avoid detection,” Malwarebytes’ Jérôme Segura said.
While malvertising campaigns are known to set up replica sites advertising widely-used software, the latest activity marks a deviation in that the website mimics WindowsReport[.]com.
The goal is to trick unsuspecting users searching for CPU-Z on search engines like Google by serving malicious ads that, when clicked, redirect them to the fake portal (workspace-app[.]online).
At the same time, users who are not the intended victims of the campaign are served an innocuous blog with different articles, a technique known as cloaking.
The signed MSI installer that’s hosted on the rogue website contains a malicious PowerShell script, a loader known as FakeBat (aka EugenLoader), which serves as a conduit to deploy RedLine Stealer on the compromised host.
“It is possible the threat actor chose to create a decoy site looking like Windows Report because many software utilities are often downloaded from such portals instead of their official web page,” Segura noted.
This is far from the first time deceptive Google Ads for popular software have turned out to be a malware distribution vector. Last week, cybersecurity firm eSentire disclosed details of an updated Nitrogen campaign that paves the way for a BlackCat ransomware attack.
Two other campaigns documented by the Canadian cybersecurity firm show that the drive-by download method of directing users to dubious websites has been leveraged to propagate various malware families like NetWire RAT, DarkGate, and DanaBot in recent months.
The development comes as threat actors continue to increasingly rely on adversary-in-the-middle (AiTM) phishing kits such as NakedPages, Strox, and DadSec to bypass multi-factor authentication and hijack targeted accounts.
To top it all, eSentire also called attention to a new method dubbed the Wiki-Slack attack, a user-direction attack that aims to drive victims to an attacker-controlled website by defacing the end of the first para of a Wikipedia article and sharing it on Slack.
Specifically, it exploits a quirk in Slack that “mishandle[s] the whitespace between the first and second paragraph” to auto-generate a link when the Wikipedia URL is rendered as a preview in the enterprise messaging platform.
It’s worth pointing out that a key prerequisite to pulling off this attack is that the first word of the second paragraph in the Wikipedia article must be a top-level domain (e.g., in, at, com, or net) and that the two paragraphs should appear within the first 100 words of the article.
With these restrictions, a threat could weaponize this behavior such that the way Slack formats the shared page’s preview results points to a malicious link that, upon clicking, takes the victim to a booby-trapped site.
“If one does not have ethical guardrails, they can augment the attack surface of the Wiki-Slack attack by editing Wikipedia pages of interest to deface it,” eSentire said.
Reference: https://thehackernews.com/2023/11/new-malvertising-campaign-uses-fake.html